Hard disk encryption is critical to data security: here's what you need to know
The exponential rise of cybercrime has led to the growth of encryption solutions. At the same time, there has been a push back from governments. Let's explore what hard disk encryption is and why it's critical to business relevance.
In recent weeks, there’s been much talk about encryption. Ever since the Trump administration started their campaign against cryptography, even the mainstream media has started exploring this topic.
However, this is only the beginning. As our digital security grows more critical by the second, you can be sure to hear a lot more about it.
This is because encryption is now vital to protect sensitive personal and business data. But before we get ahead of ourselves, let’s define it.
What’s encryption?
The original idea behind encryption isn’t limited to technology. It was first used by ancient communities in Egypt and Greece to encode secret messages that couldn’t be read by “the enemy.”
Today, encryption can be described as a method of turning plain text into a scrambled unintelligible format (known as cipher) by leveraging different algorithms.
So even in the event of a data breach, that information will not be accessible to hackers. In this scenario, you can’t decipher the encoded data without a decryption key.
Encryption is now widely used across the following industries:
- Cloud storage
- Communication apps
- E-commerce
- Healthcare
- Online banking
What are the key benefits of encryption?
The primary benefits of encryption are privacy and robust security. Encryption solutions can be used to secure data at rest (where it lives) or in motion (when it’s in transit).
This approach ensures that the data is unreadable even if hackers compromise it while it’s in transit. At present, there’s no better method of ensuring data privacy and security.
The Advanced Encryption Standard (AES)
As cybercrime grew exponentially, governments had to step in to improve security standards against advanced hacking techniques. Today, the top-security standard is AES, and it was set up by the U.S. National Institute of Standards and Technology.
AES has a strong reputation for its resilience to cyberattacks. When data is encrypted following the AES approach, multiple security keys will be required to retrieve the data back in its original form.
So it’s no surprise that it’s the go-to tool for used by security services, governments, financial institutions, and other leading multinationals.
256-Bit
256-bit encryption can be described as a process where data or files are encrypted by leveraging a 256-bit key to achieve total encryption. It’s more secure than previous incarnations that used 128-bit and 192-bit encryption algorithms.
This is an effective response to multi-pronged brute force attacks because every bit that’s added will double the number of possible keys. As a result, there will be an infinite number of key variations generated to help secure sensitive information.
It’s highly effective because the time, resources, and sheer computing power needed to try every possible key variation would take over a billion years (and that’s to breach a 128-bit key encryption).
XTS
The AES approach to encryption is called block cipher. In this scenario, data is divided into 128-blocks before it’s scrambled with 256-bit keys.
When you follow this method, the disks will store data in a particular way, and disk sectors will be divided into blocks. These will be the same size as blocks encrypted by the block cipher.
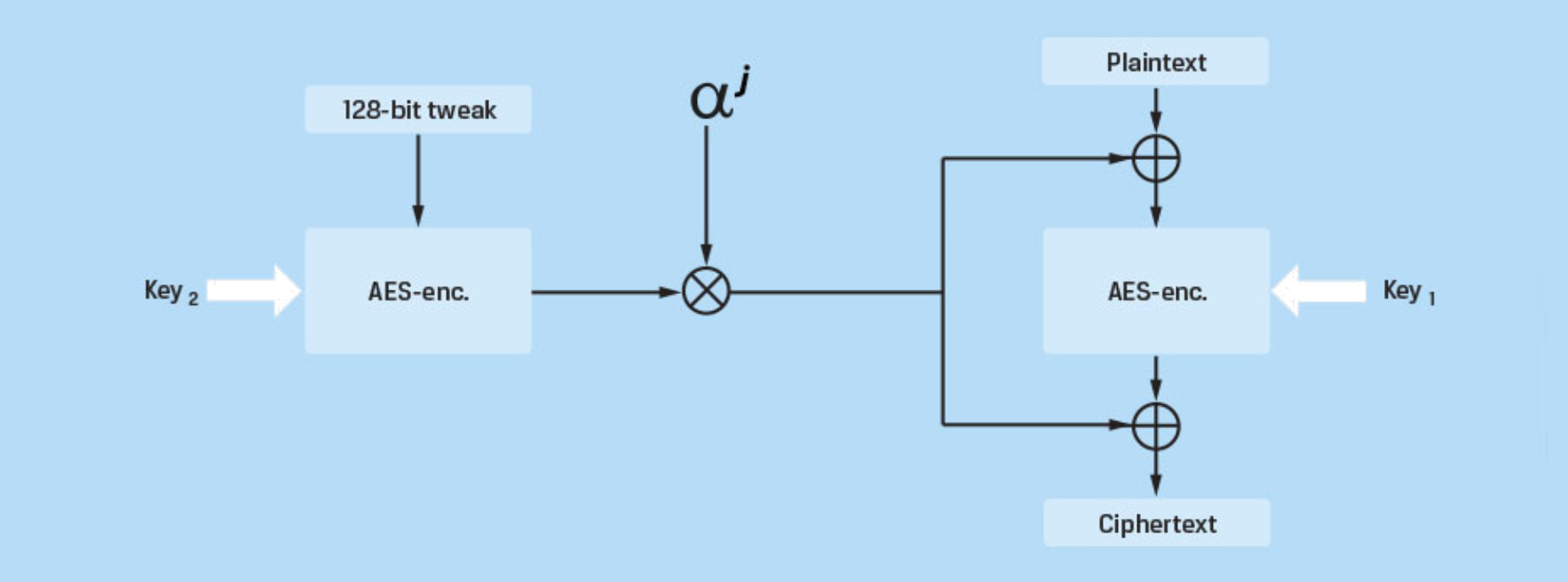
(Source).
When you follow the XTS approach, the scrambling process will include 14 rounds of encryption to make data completely unrecognizable. So whenever you leverage XTS block cipher mode, your organization will benefit from guaranteed full-disk encryption.
AES 256-Bit XTS
The AES 256-Bit XTS approach to encryption ties all these robust security solutions together. As described in the NIST special publication SP 800-38E, the XTS algorithm will be used to encrypt data on the drive platter.
When sensitive data demands extra levels of protection, the go-to approach to data encryption is AES 256-Bit XTS data encryption.
Below you will find some examples of how AES 256-Bit XTS is applied to encrypt portable drives, server disks, and servers:
Portable disks
Anyone can encrypt a portable disk. But if this proves to be a challenge, you can use the services of third-party providers.
Robust encryption can be deployed across storage devices like the following:
- Flash Drives (USBs)
- Hard Disk Drive (HDDs)
- Solid State Drives (SSDs)
Server disks
AES 256-Bit XTS encryption can also be deployed across server disks. You can encrypt the data at rest on the physical hard drive, seamlessly. You won’t need to set up any additional Hardware Security Modules or Key Management Servers.
HPE Secure Encryption is a leading security solution that’s used to secure data at rest. It’s the perfect tool for bulk storage hard drives and SSDs (as long as they’re connected to a compatible HPE Smart Array Controller). The encryption and decryption keys can be efficiently managed at a BIOS level.
What about virtual servers?
This same approach to encryption can be deployed seamlessly on virtual servers leveraging robust security tools like vSAN encryption.
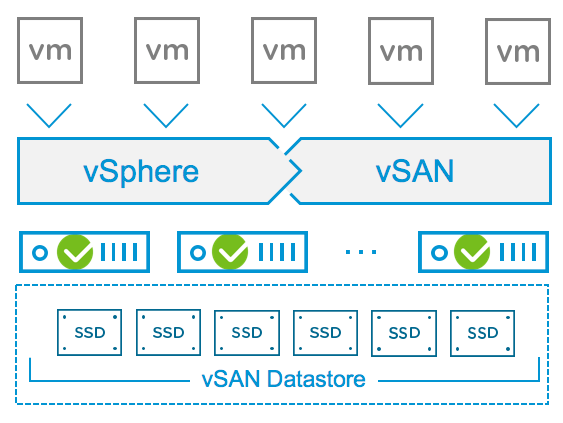
(Source).
Alternatively, you can also use logical volume hard disk encryption software from the likes of Bitlocker to secure your sensitive data. It’s a popular encryption solution that comes with recent versions of the Windows operating system.
On the cloud, all these different encryption methods can be deployed to secure personal and enterprise data. This is because although it’s called the “cloud,” your data will live in secure data centers on physical hardware.
While governments might want to access your sensitive data under the guise of national security, it's essential to consider the fact that any backdoor will also provide an opportunity for hackers to steal your personally identifiable information.
That's why encryption remains the only viable solution that can help keep both enterprise data and personal data safe and secure.
To learn more about how encryption can help ensure the security of your digital assets, schedule a call with one of our in-house data security experts.